Decentralized MPC
Overview
Decentralized MPC is not just about strengthening security - it's about redesigning how we manage access to digital assets and digital identity. At its core, Decentralized MPC represents a shift from thinking about “who holds the key” to “how the key is held.” This subtle but profound change unlocks new possibilities for secure, collaborative, and censorship-resistant control of digital assets. It is not just an improvement over traditional key management but a reimagining of trust itself, enabling systems where cryptography and decentralization merge to create a foundation for scalable, composable, and self-sovereign digital infrastructures.
What is a Decentralized MPC Wallet?
A Decentralized MPC Wallet is a next-generation digital wallet architecture where the private key is split and distributed among independent nodes that operate without any central coordinator. Unlike traditional custodial or semi-centralized MPC systems where a trusted party orchestrates the signing process, Decentralized MPC wallets rely on peer-to-peer protocols and often integrate with blockchains, DAOs, or decentralized networks to manage coordination, key generation, and signature aggregation.
Key properties include:
- No single point of failure or trust
- Distributed key generation (DKG) with verifiable secret sharing (VSS/PVSS)
- Threshold signing (TSS) executed among peers
- Programmable coordination via smart contracts or decentralized identity systems
- Enhanced resilience, censorship-resistance, and suitability for DAO treasury management, social recovery, and non-custodial key management
In essence, Decentralized MPC wallets combine the security of MPC cryptography with the trust model of decentralized networks, enabling self-sovereign, composable, and non-custodial wallets that scale from individuals to large organizations.
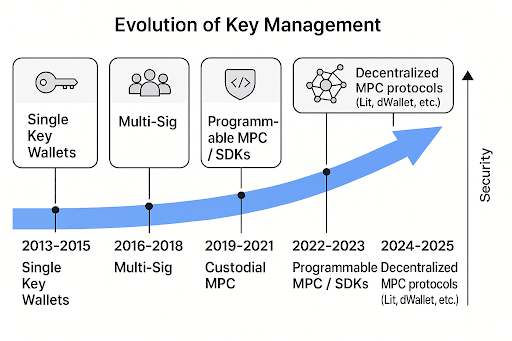
Evolution of MPC Key Management
Multiparty Computation (MPC) has its roots in academic research dating back to the 1980s. It emerged from the desire to compute functions over private data without revealing it. Here's how it evolved into a critical cryptographic primitive in blockchain:
With an expanding blockchain world, trustless infrastructure is no longer an attractive aspiration but a necessary one. Decentralized MPC in this sense is not merely a cryptographic curiosity but a transformative approach to key management. Traditional MPC solutions have, by and large, relied on central coordinators to handle key-generation and signature protocols. However, what if we simply eliminated the middleman? Decentralized MPC solves this problem by using peer-to-peer topology. Keys are distributed securely among participants, minimizing the risk of compromise and reducing the need to trust any single party.
Why Decentralization is Important for MPC
MPC is no longer an edge-case product. Fireblocks and Coinbase scale it in large organizations. Such products inevitably need a trusted orchestrator in the background, and this is a small but considerable centralization risk. Shifting to a decentralized MPC addresses three key concerns:
-
Reduced Trust Assumptions: With no single coordinator, there's no central party that can be compromised.
-
More Resilience to Censorship: Decentralized networks are more difficult to shut down or control.
-
Better Composability: Decentralized autonomous organizations, cross-chain dapps, and wallets can now plug into the decentralized MPC as security modules directly.
In fact, decentralization is not a thought experiment but really an operational necessity. Decentralization brings new custody, authorization, and governance, making digital assets significantly safer and more interoperable.
The Cryptographic Building Blocks behind Decentralized MPC
Consolidating decentralized MPC systems involves integrating a notable number of cryptographic and networking technologies. Let us list the most important components:
-
Distributed Key Generation (DKG): enables a set of participants to generate a public/private keypair such that no single entity knows the complete private key.
-
Threshold Signature Schemes (TSS): enable any t of n participants to generate an appropriate signature without needing to rebuild the secret key.
-
Verifiable Secret Sharing (VSS): a protocol that enables participants to share secrets in a way that allows verification of the correctness and consistency of their shares.
-
Gossip and Overlay Networks are rooted primarily on peer discovery and message diffusion to provide decentralized coordination.
-
Signature Aggregation & Blame Protocols: they help detect and isolate malicious or faulty nodes during the signature process.
These primitives altogether form a decent base for decentralized MPC operations, such as wallets, bridges, and others. The main system supporting MPC wallets is a complex blend of threshold cryptography and distributed key generation (DKG). These advanced cryptography components are making online transactions safer and more secure.

DKG is a cryptographic protocol designed to generate a private key into multiple shares, among a set of distributed participants. This division is done in such a way that no single participant possesses the entire key. Instead, each participant possesses a portion, or "share," of the key in such a manner that the entire key never exists in a single place at any given time. This method greatly reduces the risk of key compromise since an attacker would have to acquire numerous shares from a variety of individuals to assemble the entire key.
Threshold cryptography extends DKG by specifying a rule, or "threshold," of how many parties, or their key shares, are required to perform some action, such as signing of a transaction. For instance, in a threshold t out of n parties setup, any t parties can meet together and produce a valid signature for a transaction, but fewer than t cannot. This ensures that participating parties cannot act independently, making the system secure and collaborative.
Employing both DKG and threshold cryptography in MPC wallets ensures that a transaction can be approved only if people collaborate. Each participant contributes a share of the key to generate an authentic transaction signature. Decentralized MPC wallets use cryptographic protocols that make transactions not only secure but also transparent and credible. This ensures that the digital asset system remains authentic, verifiable, and maintains its integrity.
Decentralized MPC solutions
Decentralized MPC applications are not just theoretical - it's picking up real-world traction in several key areas:
-
User-Controlled Wallets: No single point of compromise. Users retain full control without managing raw private keys.
-
Cross-Chain Signing and Bridges: Decentralized key management for security in multi-chain operations.
-
DAO Treasury Management: Enables clear, distributed control of funds between blockchains.
-
Enterprise Custody Workflows: Policy-based signing within departments and jurisdictions.

Promising Players in the Decentralized MPC Ecosystem are:
-
Lit Protocol
-
Presently in mainnet beta.
-
Offers programmable key management via a decentralized node network, enabling use cases like gasless transactions, social recovery, and composable on-chain/off-chain encryption.
-
-
dWallet (Odsy Network)
-
Two-share MPC model.
-
Uses a user-controlled share and an MPC-controlled share to avoid collusion, while enabling programmable wallet permissions at the protocol level.
-
-
Silence Labs
-
MPC-based MetaMask Snap.
-
Provides 2FA-like security for Web3 wallets using MPC, enhancing wallet safety without altering user experience.
-
-
Entropy.xyz
-
Bleeding edge MPC library.
-
Recently released a developer library for decentralized randomness and signing, targeting scalable MPC randomness beacons.
-
-
Internet Computer Protocol (ICP)
-
Threshold ECDSA for cross-chain.
-
Uses threshold ECDSA signing with the Oisy Wallet, enabling direct smart contract signing on Bitcoin and other chains from within ICP canisters.
-
-
ARPA Network
-
Cross-chain MPC/TSS protocols.
-
Supports EVM chains with a focus on secure multi-party computation and cross-chain threshold signature schemes for DeFi and enterprise integrations.
-
-
Nillion
-
Open-source MPC tooling.
-
Developing decentralized MPC infrastructure focused on data privacy, verifiability, and scalability, aiming to power Web3 data marketplaces and confidential computing.
-
-
Passport Protocol by 0xPass
-
Composable wallet abstraction.
-
Public project for EVM wallets, introducing key management abstractions that could extend to Bitcoin and Layer-2 solutions for programmable ownership.
-
-
ContinuumDAO
-
Public-good MPC governance.
-
First to propose a fully decentralized MPC network governed via DAO voting, ensuring community-owned and censorship-resistant key management infrastructure.
-
-
Safeheron
-
Enterprise-grade MPC custody.
-
Provides secure, auditable, and customizable MPC solutions for wallets and exchanges, focusing on institutional adoption with open auditing capabilities.
-
Each of these projects tackles decentralization in its own way. They show that there is no single architecture, but there is shared interest across the ecosystem.
A look into the future of Trustless Key Management and Decentralized MPC Wallet Projects (2024–2025)
| # | Project Name | Use Cases | Key Features | Chains Supported | Development Stage |
|---|---|---|---|---|---|
| 1 | ZenGo X-MPC* | Non-custodial wallet, Seedless UX, Consumer MPC | 2-of-2 TSS, Seedless recovery, Keyless signing | Bitcoin, Ethereum, Tezos, Polygon | Mainnet (fully live and usable on public networks) |
| 2 | Lit Protocol | Decentralized key access, PKP signing, Session auth for dApps | Programmable Key Pairs (PKPs), Lit Actions, Decentralized RL signing | Ethereum, Polygon, Solana* (experimental) | Mainnet (fully live and usable on public networks) |
| 3 | dWallet (Odsy) | Smart wallet APIs, Embedded MPC in apps, Partial custody for users | Non-collusive MPC, Node-auth enforcement, Odsy Wallet SDK | EVM-compatible (ETH, BSC, etc.) | Alpha Testnet (in limited test deployments) |
| 4 | Silence Labs | 2FA MPC wallets, MetaMask Snap enhancements | MPC key signing, Biometric fallback, Device-level control | EVM-first, Expanding | Beta (in public beta test deployments) |
| 5 | Entropy.xyz | Infrastructure for cryptographic MPC, Developer tooling | Threshold ECDSA, Signature aggregation, Key gen toolkits | Blockchain-agnostic | R&D / Dev Preview (MVP, early testing, or development) |
| 6 | ZeroDev | Smart accounts, MPC-based embedded wallets for dApps | MPC, Account abstraction, Bundler infrastructure | Ethereum + L2s | Mainnet (fully live and usable on public networks) |
| 7 | 0xPass (Passport Protocol) | Developer-focused wallet infra, MPC for OAuth-based logins | OAuth + MPC, Wallet sessioning, Embedded SDK | EVM-first (ETH, Polygon, Arbitrum) | Testnet (public beta or limited test deployments) |
| 8 | Fireblocks (DeFi MPC) | Institutional custody, DeFi trading with secure MPC key management | Threshold MPC, Policy engines, Governance controls | Ethereum, Solana, Algorand, others | Enterprise Production |
| 9 | Web3Auth x MPC-TSS | Social login + MPC wallets, User onboarding | TSS, OAuth login, Web2 ↔ Web3 user flows | Ethereum, Solana, BNB Chain | Mainnet (fully live and usable on public networks) |
| 10 | Safeheron | Enterprise MPC wallet infrastructure | Multi-layer MPC, risk control systems, compliance support | Multichain (ETH, BTC, TRX, etc.) | Production (for Private Clients) |
Challenges & Open Questions
Despite the momentum, a number of significant challenges remain to be addressed:
-
Peer Discovery and Coordination: Decentralized networks have to find one another, get in sync, and collaborate without central servers.
-
Latency: Multi-round signature creation is adding complexity, which might impact UX.
-
Participant Availability: Reaching quorum when nodes are offline isn't a trivial problem.
-
Chain Interoperability: Support outside of EVM chains is still nascent.
-
Economic Incentives : Why should nodes even exist in the first place? Monetization frameworks are anemic.
-
Legal Uncertainty: Liability and compliance at best ambiguous in decentralized mode.
These issues will not be solved by technical ingenuity alone, but by concerted system-level effort.
Outlook & What Comes Next
In big ways, Decentralized MPC is just beginning and its potential is evident. It is positioned to become a key building block of the next generation of decentralized infrastructure, enabling secure and flexible key management without trusted intermediaries. We see several trends accelerating its adoption:
-
Native Chain-Level MPC Support: Emerging blockchains now integrate native MPC verification, simplifying integration and reducing computational overhead.
-
New Incentive Layers: Token-based economies are being designed to incentivize honest participation by MPC nodes, strengthening network security and decentralization.
-
Post-Quantum Resilience: Quantum-resistant multiparty schemes are under active development, future-proofing key management and signing against quantum adversaries.
-
Composable Middleware: MPC is evolving into a plug-and-play module for dApps, enabling developers to embed secure signing, encryption, and access control without rebuilding core cryptography.
-
User-Centric Access Control: Biometric proofs, social recovery, and programmable policies are being layered on top of MPC protocols, bridging security and user experience.
For our Crypto Processor project, these trends confirm our architectural decisions. By adopting Decentralized MPC, we position ourselves to leverage native chain-level integrations, build incentive-aligned key management layers, and offer our users the highest levels of security and ownership guarantees. As the ecosystem matures, Decentralized MPC will not just be an added security layer, but a core module powering secure, modular, and composable transaction signing and asset control across all supported chains.
Summary
In future iterations of MPC protocols, responsibility for generating and managing key shares will shift from a predefined group of participants to a decentralized network of nodes. Keys will be distributed among these nodes, and transaction signing will only be possible if certain access conditions are met and a designated quorum agrees to proceed.
If such networks are open-source and permissionless, they can serve as a transparent, trustless foundation for building applications like crypto wallets, removing the need for centralized intermediaries. This decentralization enhances security by eliminating single points of failure and introduces programmable key management directly into the infrastructure layer.
For our Crypto Processor project, Decentralized MPC provides a crucial architectural component: it enables secure, user-controlled key management with flexible access policies, while maintaining fast signing performance and scalability. It also aligns with our mission to build infrastructure that is censorship-resistant, modular, and interoperable across chains.
By integrating Decentralized MPC, we are ensuring that ownership, recovery, and signing logic remain fully decentralized – a foundational pillar of the next generation of blockchain applications.